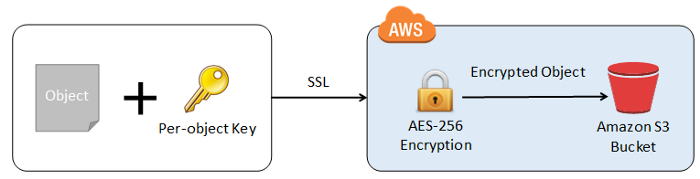
Following with our HIPAA recommendations, another step we need to do on our cloud infrastructure to secure our data for HIPAA is data at rest encryption.
In case you are using AWS S3 buckets to store PHI data, follow the instructions below to have that data encrypted.
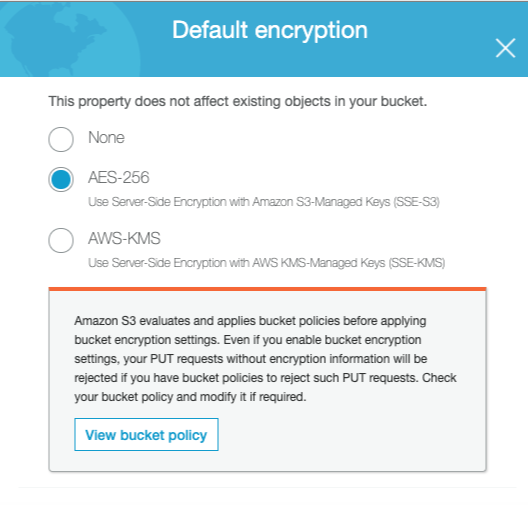
Instructions
- Login to AWS management console and go to S3 section
- Choose the bucket that corresponds to your application
- Go to properties → Default encryption
- Choose AES-256
- Save
Enabling default encryption doesn’t change the encryption of objects that are already in the bucket. After you enable default encryption, the encryption that you set applies only to future uploads. For example, if you enable server-side encryption with AWS KMS (SSE-KMS) on the bucket, then any unencrypted objects already in the bucket remain unencrypted. Additionally, any objects already encrypted using Amazon S3-managed keys (SSE-S3) remain encrypted with SSE-S3.
To change the encryption of an existing object to SSE-KMS, you have a couple of options. The first option is to re-upload the object, which involves downloading the object from the S3 bucket, encrypting it with SSE-KMS, and then uploading it back to the bucket. This ensures that the object is encrypted using the desired encryption method.
The second option is to copy the object over itself. This can be done by using the AWS CLI or the S3 console. When you copy the object, you have the option to specify the encryption method as SSE-KMS. By choosing this option, the object will be copied to the same bucket but with the desired encryption.
Both options provide a way to update the encryption of existing objects to meet the HIPAA requirements for data at rest encryption. It is important to note that these options only apply to objects that are already in the bucket, and any new uploads will automatically be encrypted with the chosen encryption method.
Using CLI the command to encrypt all existent objects would be something like this:
aws s3 cp s3://bucket-name/ s3://bucket-name/ — recursive — sse